Le déploiement et l'administration d'applications Java/JEE sont des activités essentielles pour les développeurs et les équipes informatiques. Ces tâches peuvent être complexes, c'est pourquoi il est nécessaire de bien connaître

Dans le monde d'aujourd'hui, les compétences en informatique sont devenues indispensables pour réussir dans presque tous les domaines. Pour ceux qui souhaitent développer leurs connaissances et cherchent des conseils pour

Le succès d'un site e-commerce repose en grande partie sur son design. Une interface accueillante et fonctionnelle augmente les chances de faire des ventes et
Le commerce en ligne offre d'innombrables opportunités pour réussir dans le monde des affaires. Mais pour tirer profit de la croissance exponentielle du marché, il

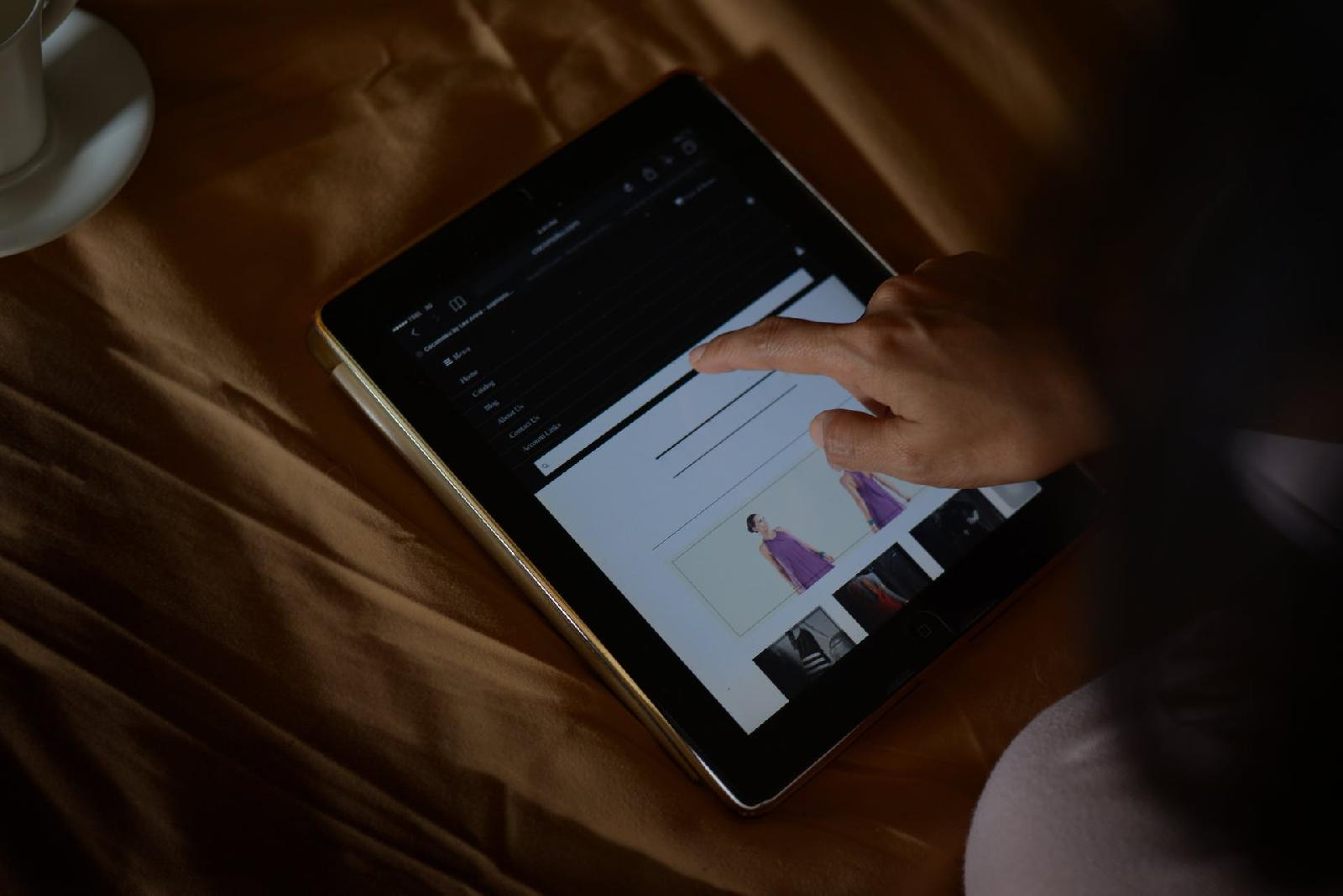
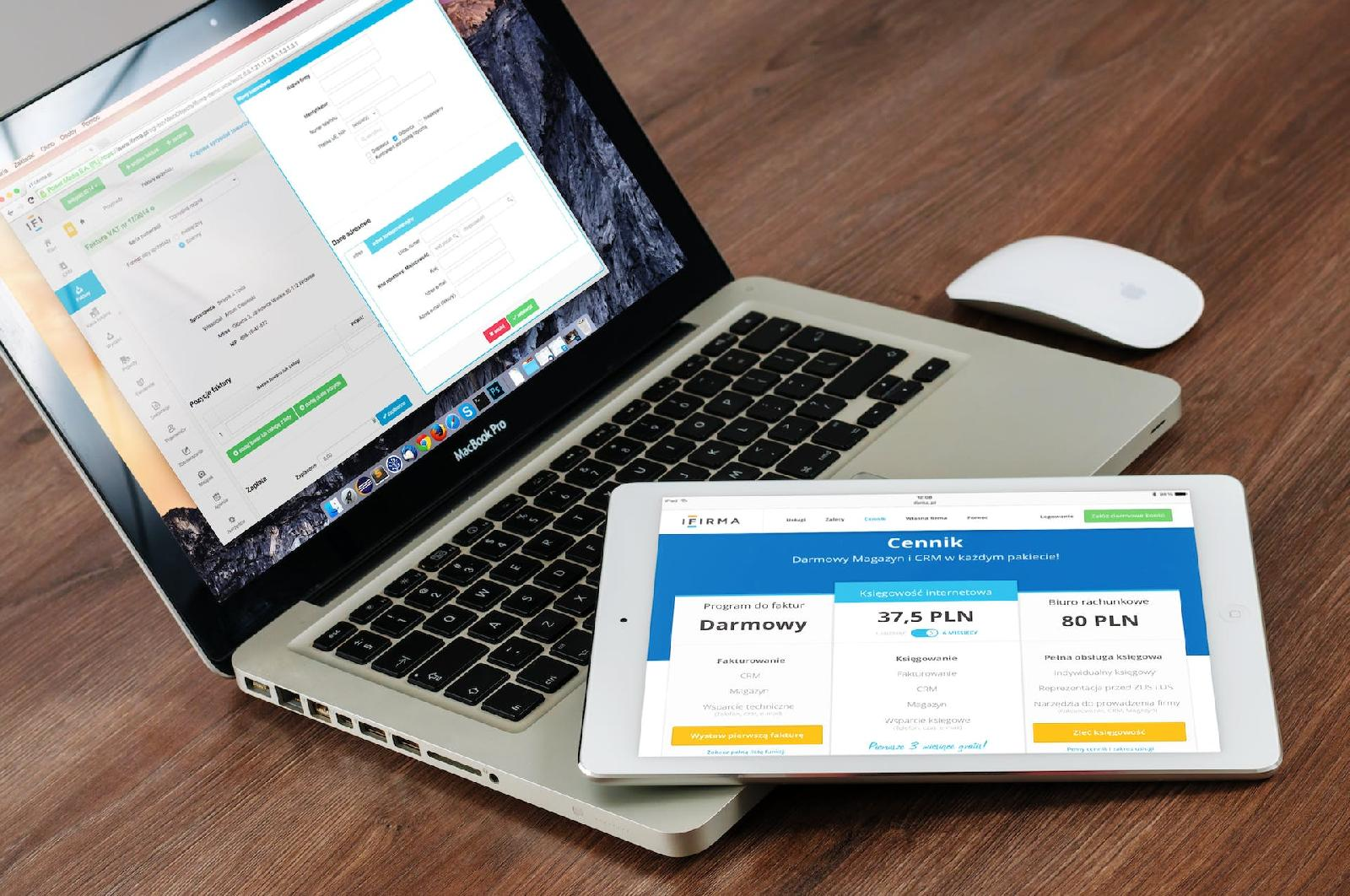
Dans le monde du commerce électronique, la concurrence est rude. Pour réussir, il est essentiel de disposer d'un site web puissant et rentable. De nombreuses

Dans le monde du e-commerce, choisir la solution de paiement adaptée à sa plateforme est primordial. Parmi les différentes options disponibles, Stripe se présente comme


Dans notre ère numérique, apprécier l'art et la culture est désormais à portée de clics.
Le commerce électronique a connu une croissance exponentielle ces dernières années. Pour réussir à vendre

Dans la vie d'un auto-entrepreneur du web, l'une des premières questions qui se posent est celle de la fixation du taux horaire. Comment être sûr